Could emerging tech present new forensics in the suspicious early demise of controversial Rolling Stone reporter, Michael Hastings? How cheaper hardware and open-sourced coding could shed new light on a murder as the possibility of remotely hacking today’s cars gains traction.
Hacking your car might already be possible. This tweet by NYT tech writer, Nick Bilton, is a great example:
Just saw 2 kids walk up to my LOCKED car, press a button on a device which unlocked the car, and broke in. So much for our keyless future.
— Nick Bilton (@nickbilton) April 6, 2015
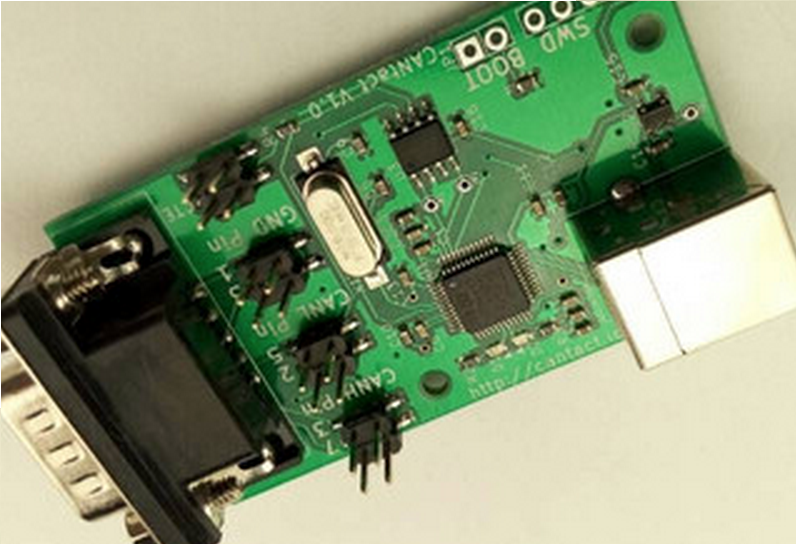
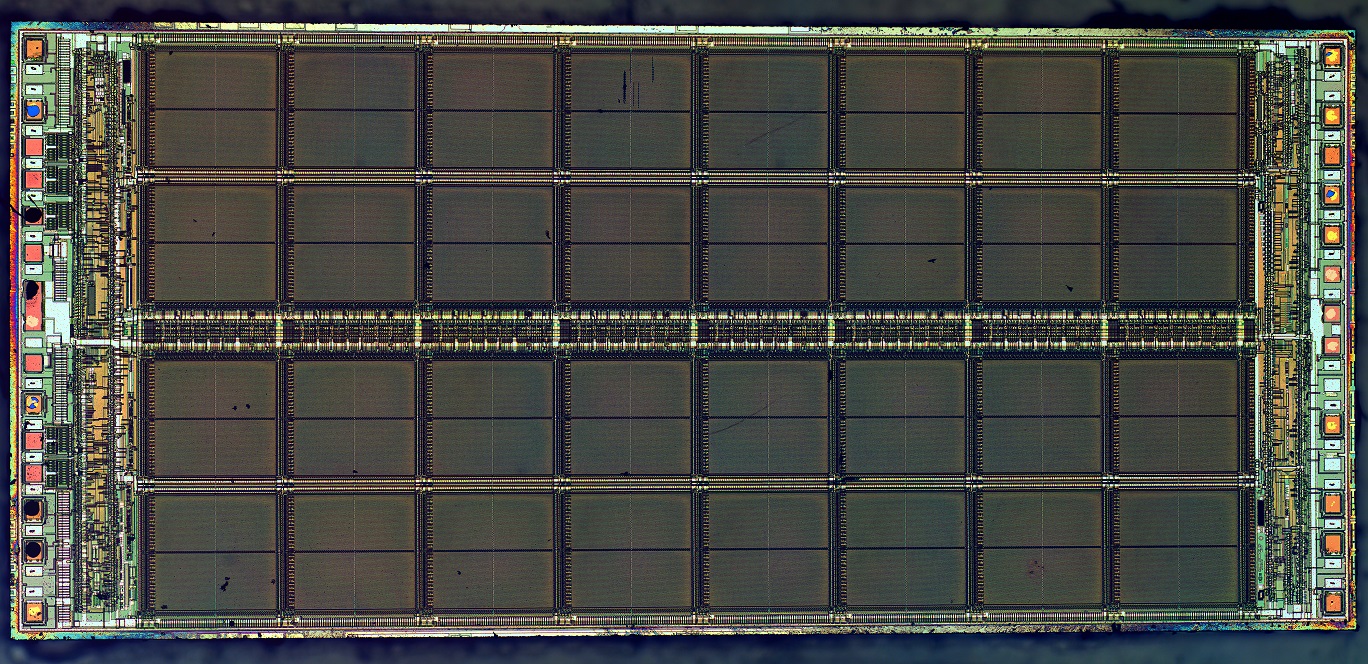
Weeks back, I wrote a short piece about CANtact, a $60 device that enables you to interface with a car’s onboard computer through your laptop’s USB port. Eric Evenchick presented CANtact at Black Hat Asia 2015 security conference in Singapore. The onboard CPU of a motor-vehicle is called the CAN, for Controller Area Network. Evenchick hopes his device’s affordability will spur programmers to reverse engineer the firmware and proprietary languages various CAN systems use.
Read more about CANtact: CANtact Device Lets you Hack a Car’s CPU for $60
I got feedback on the CANtact story about a seemingly unrelated topic: The Death of Michael Hastings. Hastings was Rolling Stone and Buzzfeed contributor who became very vocal about the surveillance state when the U.S. Department of Justice started investigating reporters in 2013. Hastings coined the term “war on journalism” when the Obama Administration sanctioned limitations on journalists ability to report when the White House considered it a security risk. Buzzfeed ran his last story, “Why Democrats Love to Spy On Americans”, June 7, 2013. Hastings is considered suspicious by many Americans after he died in an explosive, high -speed automobile accident, June 18, 2013, in Los Angeles, CA.
Check out one of the last interviews with Michael Hastings and scroll down for a description of the oft repeated conspiracy theory surrounding his untimely death.
The Michael Hastings Conspiracy Theory:
Unlike a lot of post-millennium conspiracy theories, which usually start online, this one actually began on television. Reporters were already contentious about the limitations the Obama admin. were attempting to impose and it seemed like extremely suspicious timing that one of the leaders of the criticism against censorship was suddenly killed. The internet ran with it and some Americans considered the crash as suspicious at the time. Public opinion is often without the merit of hard evidence, though, and this case was no different. Not everyone considered the media coverage unbiased, considering the political stake journalists had in the issue.
The first solid argument that Hasting didn’t die by accident came from Richard A. Clarke, a former U.S. National Coordinator for Security, Infrastructure Protection, and Counter-terrorism(what a title~!), who called the crash “consistent with a car cyber attack”. The conspiracy theory gestating around water coolers and message boards was truly born when Clarke went public with this outright accusation:
“There is reason to believe that intelligence agencies for major powers—including the United States—know how to remotely seize control of a car. So if there were a cyber attack on [Hastings’] car—and I’m not saying there was, I think whoever did it would probably get away with it.”
Next, WikiLeaks announced that Hastings reached out to a Wikileaks lawyer Jennifer Robinson only a few hours before the crash.
Army Staff Sergent Joe Biggs came forward with an email he thought might help in a murder investigation. The email was CCed to a few of Hastings’ colleagues, stating he was “onto a big story” and planned to “go off the radar”. Perhaps the most incriminating detail is that he warned the addressees of this email to expect a visit from the FBI. The FBI denied Hastings was being investigated in a formal press release.
LA Weekly admitted Hastings was preparing a new installment of what had been an ongoing story involving the CIA. Hastings’ wife, Elise Jordan, confirmed he had been working on a story profiling CIA Director John O. Brennan.
The case against foul play:
I have to admit, I got sucked in for a second but Cosmoso is a science blog and I personally believe an important part of science is to maintain rational skepticism. The details I listed above are the undisputed facts. You can research online and verify them. It might seem really likely that Hastings was onto something and silenced by some sort of foul play leading to a car accident but there is no hard evidence, no smoking gun, no suspects and nothing really proving he was a victim of murder.
The rumor online has always been that there are suspicious aspects to the explosion. Cars don’t always explode when they crash but Frank Markus director of Motor Trend said the ensuing fire after the crash was consistent with most high-speed car crashes. The usual conspiracy theorist reaction is to suspect this kind of testimony to have some advantage or involvement thus “proving” it biased. It’s pretty difficult to do that in the case of Frank Markus, who just directs a magazine and website about cars.
Hastings’ own family doesn’t seem to think the death was suspicious. His brother, Jonathan, later revealed Michael seemed “manic” in the days leading up to the crash. Elise Jordan, his wife told the press it was “just a really tragic accident”
A host of The Young Turks who was close with Hastings once said Hastings’ friends had noticed he was agitated and tense. Michael often complained that he was being followed and watched. It’s easy to dismiss the conspiracy theory when you consider it may have stemmed from the line of work he chose.
Maybe the government conspiracy angle is red herring.
Reporting on the FBI, the Military, the Whitehouse, or the CIA are what reporters do. People did it before and since. Those government organizations have accountability in ways that would make an assassination pretty unlikely.
If it wasn’t the government who would have wanted to kill Hastings?
A lot of people, it turns out. Hastings had publicly confirmed he received several death-threats after his infamous Rolling Stone article criticizing and exposing General McChrystal. Considering the United States long history of reactionary violence an alternate theory is that military personnel performed an unsanctioned hit on Hastings during a time when many right wing Americans considered the journalist unpatriotic.
Here’s where the tech comes into play:
Hastings had told USA Today his car had recently been “tampered with”, without any real explanation of what that means but most people in 2013 would assume it means physical tampering with the brakes or planting a bug. In any case he said he was scared and planned to leave town.
Now it’s only two years later, and people are starting to see how a little bit of inside knowledge of how the CAN computer works in a modern vehicle can be used to do some serious harm. We might never know if this was a murder, an assassination or an accident but hacking a car remotely seemed like a joke at the time; two years later no one is laughing.
|
Jonathan Howard
Jonathan is a freelance writer living in Brooklyn, NY |